Fortify Your Online Security: Choosing The Best Two-Factor Authentication Apps
Digital age, securing online accounts is more important than ever, as cyber threats like hacking, phishing, and password breaches continue to rise. One of the most effective ways to enhance security is through Two-Factor Authentication (2FA). This method adds an extra layer of protection by requiring users to verify their identity using two different forms of authentication.
While passwords alone can be compromised, 2FA significantly reduces the risk of unauthorized access by combining something the user knows (like a password) with something they have (such as a one-time code or biometric verification). With various 2FA apps available, choosing the right one is crucial for maintaining both security and convenience. This article explores how 2FA works, the best authentication apps, and key considerations for selecting the most suitable option to fortify your online security.
What is Two-Factor Authentication?
Two-Factor Authentication (2FA) is a security process that requires users to provide two different forms of verification to access an account or system. It adds an extra layer of protection beyond just a password, making it harder for unauthorized users to gain access. Typically, 2FA involves something the user knows, like a password, and something they have, such as a one-time code sent to their phone or email. In some cases, biometric authentication, like fingerprints or facial recognition, can be used as the second factor. By requiring two separate authentication methods, 2FA helps protect sensitive information from hackers, phishing attacks, and unauthorized access.
The Importance of Two-Factor Authentication

Digital age, simple passwords no longer provide sufficient security against the myriad cyber threats that target online accounts. Cybercriminals have developed sophisticated methods to bypass single-layer security measures, from phishing scams to brute force attacks. Two-factor authentication provides an additional security barrier by requiring something you know (like a password) and something you have (such as a mobile device for receiving or generating codes). This means that even if a hacker gains access to your password, they would still need the second factor to breach your account, drastically reducing the likelihood of unauthorized access.
How Two-Factor Authentication Works
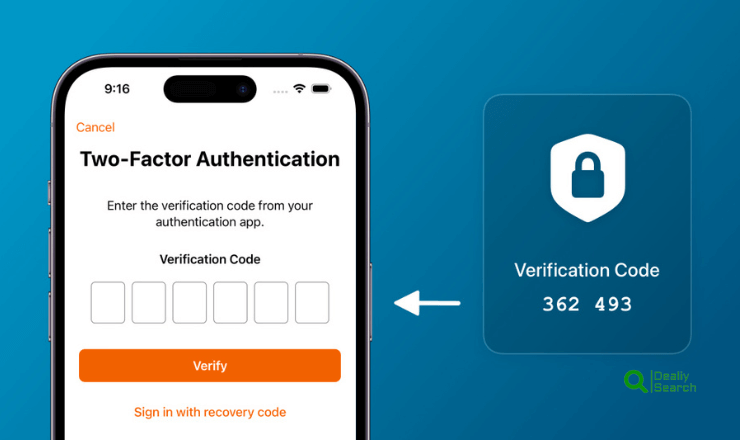
Two-Factor Authentication (2FA) enhances security by requiring users to provide two different forms of verification before accessing an account or system. The process typically begins when a user enters their username and password. Once this step is completed, a second authentication factor is required, which can be something the user knows (a PIN or security question), something they have (a one-time code sent via SMS, an authenticator app, or a hardware token), or something they are (biometric authentication like fingerprints or facial recognition).
This extra layer of security helps prevent unauthorized access, even if an attacker steals the user’s password. Many 2FA systems use time-based one-time passwords (TOTP), which are valid for only a short period, adding an additional safeguard against cyber threats. By combining two authentication factors, 2FA significantly reduces the risk of unauthorized access and strengthens online security.
Verification Process
Step 1: The user enters their username and password as usual.
Step 2: Instead of gaining immediate access, the user is prompted to provide a second verification method typically a code sent to their mobile device via SMS, email, or an authentication app.
Code Generation and Delivery: Authentication Apps: These apps (e.g., Google Authenticator, generate time-sensitive codes that refresh every 30 seconds to a minute.
SMS/Email Codes: A code is sent to the user’s registered phone number or email address, which they must enter to complete the login process.
Access Granted: Users gain access to their account once the correct code is entered. This process ensures that even if someone else has the password, they cannot access the account without having the second factor.
Benefits of Two-Factor Authentication
Enhanced Security: Adds a significant layer of security, making it much harder for attackers to gain unauthorized access.
Reduced Fraud Risk: This is especially beneficial in financial transactions and sensitive data access, where verifying user identity is crucial.
Regulatory Compliance: Helps businesses comply with security standards and regulations that mandate more robust access controls.
User Trust: Increases confidence among users that their accounts and personal information are well-protected.
Considerations for Implementing Two-Factor Authentication
When implementing Two-Factor Authentication (2FA), several key considerations should be taken into account to ensure both security and user convenience. First, organizations must choose the right authentication methods, such as SMS codes, authenticator apps, or biometric verification, based on security needs and user accessibility. It is also essential to provide backup authentication options in case users lose access to their primary method.
Balancing security with usability is important, as overly complex processes may discourage users from enabling 2FA. Organizations should also educate users on the importance of 2FA and how to use it effectively. Lastly, regular updates and monitoring are crucial to identify and mitigate potential vulnerabilities, ensuring that the authentication system remains secure against evolving threats.
User Convenience: While it adds a layer of security, it also requires an additional step in the login process, which may be inconvenient.
Dependency on User Devices: When the second factor involves a user’s mobile device, access to accounts can become problematic if the device is lost, stolen, or out of battery.
Phishing Vulnerabilities: SMS-based verification codes can still be intercepted or redirected via sophisticated phishing attacks. Therefore, for higher security, an authentication app that generates codes offline is often recommended.
Duo Mobile: A Secure Two-Factor Authentication App
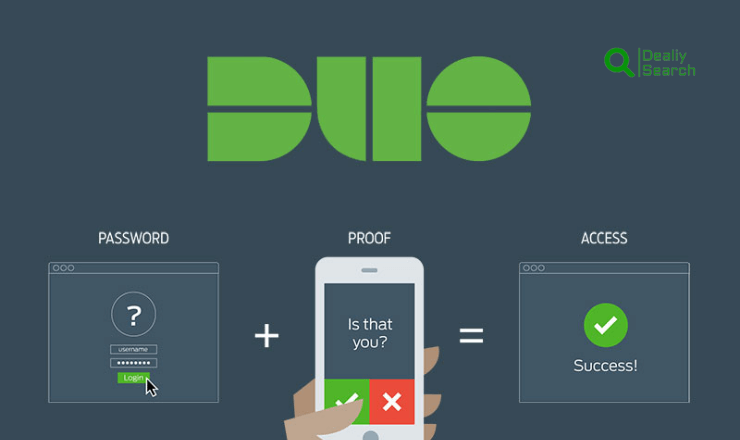
Duo Mobile is a popular two-factor authentication (2FA) app developed by Cisco, designed to enhance account security by requiring a second verification step beyond a password. It is widely used by individuals and organizations to protect sensitive data from unauthorized access.
Features of Duo Mobile
Push Notifications: Allows users to approve or deny login requests with a single tap.
Time-Based One-Time Passwords (TOTP): Generates secure codes that can be used for authentication.
Biometric Authentication: Supports fingerprint and facial recognition for added security.
Multi-Account Support: Enables users to secure multiple accounts within the app.
Offline Authentication: Provides authentication codes without requiring an internet connection.
How Duo Mobile Works
- Setup: Users link their accounts by scanning a QR code or entering a setup key.
- Login Attempt: When logging in, users receive a push notification or need to enter a TOTP code.
- Verification: The user approves the request through the app or enters the generated code to access their account.
Google Authenticator: A Reliable Two-Factor Authentication App
Google Authenticator is a widely used two-factor authentication (2FA) app developed by Google to enhance account security. It generates time-based one-time passwords (TOTP) that users enter alongside their regular passwords for an added layer of protection. The app works offline, making it a secure option even without an internet connection. Users can set it up by scanning a QR code or entering a setup key provided by the service they wish to secure.
Since it does not rely on SMS codes, it reduces the risk of SIM swapping attacks and phishing attempts. Google Authenticator supports multiple accounts, making it a convenient security solution for personal and professional use. Its simplicity, reliability, and strong encryption make it an effective tool for protecting online accounts from unauthorized access.
Choosing the Right 2FA App
Selecting the right two-factor authentication (2FA) app is crucial for balancing security, usability, and convenience. When choosing a 2FA app, users should consider factors such as security features, compatibility, and ease of use. Apps like Google Authenticator, Duo Mobile, and Microsoft Authenticator provide strong protection through time-based one-time passwords (TOTP) and push notifications. Features like biometric authentication, cloud backup, and multi-device support can enhance security and accessibility.
Offline functionality ensures authentication codes are available even without an internet connection. Organizations may also prioritize enterprise-level features, such as centralized management and integration with security policies. Ultimately, the best 2FA app should align with the user’s security needs, offering both robust protection and a seamless authentication experience.

- Security Features: Look for end-to-end encryption and secure backup options.
- Platform Compatibility: Ensure the app supports all your devices.
- User Experience: Choose apps with an intuitive interface and minimal setup.
- Backup Options: Apps like Duo Mobile offer encrypted cloud backups, providing an extra layer of security.
- Biometric Integration: Some apps allow biometric verifications, such as fingerprint or facial recognition, adding another layer of security.
Frequently Asked Question
Why is Two-Factor Authentication (2FA) Important?
Two-Factor Authentication adds an extra layer of security to online accounts by requiring a second form of verification beyond a password. This reduces the risk of unauthorized access, protecting personal and sensitive information from cyber threats such as hacking, phishing, and password breaches.
What Are the Best 2FA Apps Available?
Some of the best 2FA apps include Google Authenticator, Duo Mobile, Microsoft Authenticator, Authy, and LastPass Authenticator. These apps generate time-based one-time passwords (TOTP) or provide push notifications for secure authentication.
How Do I Choose the Right 2FA App?
When selecting a 2FA app, consider factors such as security features, multi-device support, cloud backup, offline access, and ease of use. If you need business-level security, apps like Duo Mobile and Microsoft Authenticator offer advanced management options. For personal use, Google Authenticator and Authy are popular choices.
Can 2FA Apps Work Without an Internet Connection?
Yes, most 2FA apps, such as Google Authenticator and Microsoft Authenticator, generate TOTP codes that work offline. However, push notification-based authentication (such as in Duo Mobile) requires an internet connection.
What Happens If I Lose Access to My 2FA App?
If you lose access to your 2FA app, recovery options include backup codes, cloud synchronization (available in apps like Authy), or resetting 2FA through account recovery processes. It’s crucial to store backup codes securely when setting up 2FA to prevent account lockout.
More Related Post: Essential Emergency Power Generator
Conclusion
Two-factor authentication apps are vital to securing your online presence. By choosing the right app, such as Duo Mobile, Google Authenticator, or Authy, you ensure that your accounts remain protected with an extra layer of security. Remember, the ultimate goal of using 2FA apps is to make your digital life more manageable and much safer from potential cyber threats. Stay secure by integrating these robust solutions into your security strategy today.
This blog post utilizes insights from the latest industry research and comparisons of leading 2FA solutions to guide you in strengthening your digital security framework. Whether for personal use or securing business operations, the highlighted two-factor authentication apps provide adequate defenses against the increasingly sophisticated landscape of cyber threats.